Without exaggeration, this is also the source for great threats. In the past hackers were limited to attacking computers in homes and offices but with the amazing number of devices being routinely connected to the internet, completely new possibilities are opening up for the individuals that use IoT for darker purposes.
The future is dependent on averting attacks
There are a number of current examples of IoT devices being used in a malicious way with the 2016 DDoS attack against Dyn, a major DNS provider, standing out. In the Dyn attack, hackers managed to seize control over thousands of cameras and DVRs to launch a massive DDoS attack that affected many major websites including Twitter, Netflix, Spotify, PayPal and Amazon in a single instant.
The future of IoT is dependent on our ability to make sure that attacks like the one on Dyn are impossible and, in the event that they do happen, the consequences are limited.
Most connected devices simply do not have the necessary resources to make them safe, requiring the communications solution to provide security for them. So how do we protect that which cannot protect itself?
What if we can create a calm lagoon in which devices can communicate, separated from the storm raging on the Internet?
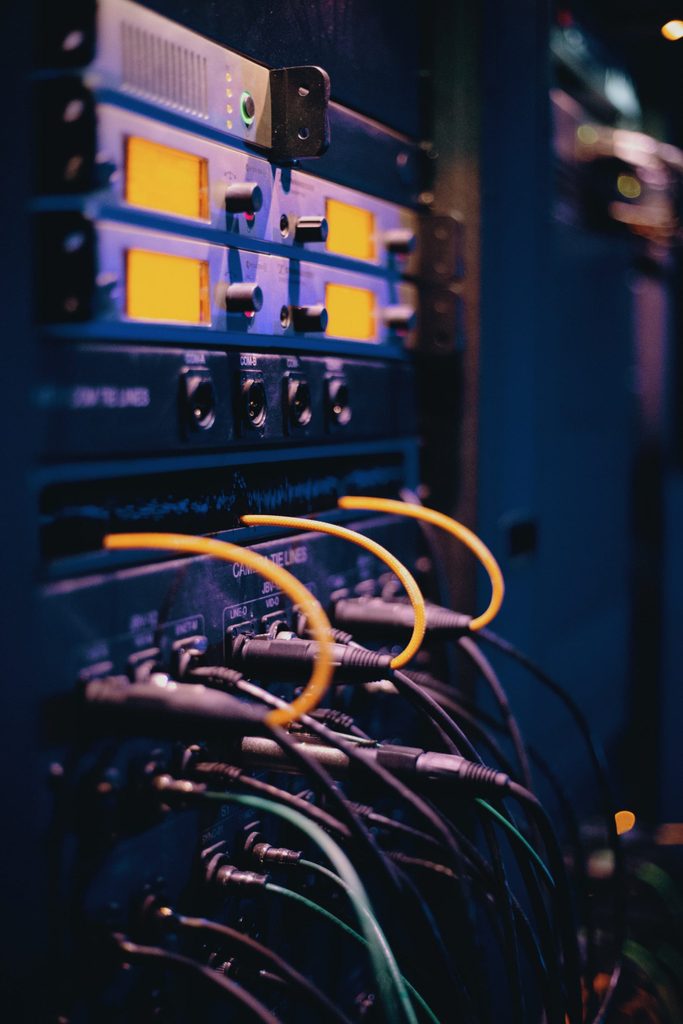
AddSecure Link: A quiet and safe lagoon
By placing IoT security in the communication layer, we secure the edges. We create a calm environment in which our devices can communicate freely, without risk of interference from the outside.
Using this approach to security, communication can provide high performance solutions that are resilient, scalable and have high availability.
It is also imperative that communication service providers have a close cooperation with major players in the security industry as well as within the ecosystem of IoT. Providers of communication and security for IoT also need to get smarter. Clever tools for cognitive analysis of data streams (the streams, not the data itself) needs to be added.
Security must be integrated into the core
What used to be the events of science fiction has partly turned into reality. We are connected, we share information, we automate functions.
However, new technology always comes with new, and very real, security threats. Security needs to move from being an afterthought, something that is added to a device, into something that is integrated into its core. A natural part of your solution.
Make sure to block threats from accessing targeted devices. Don’t leave them vulnerable on the Internet, create the calm and relax.
White paper: How to strengthen IoT security
What threats are involved with connecting devices to the Internet? And what are the vulnerabilities within the different communications technologies? Learn more about this and how to strengthen your IoT security in this white paper.
